Stolen Government Phone Exposes Lax Security Protocols, Fuels Concerns Over Bureaucratic Inefficiency
The theft of a former staffer's device raises questions about data protection and potential political fallout.

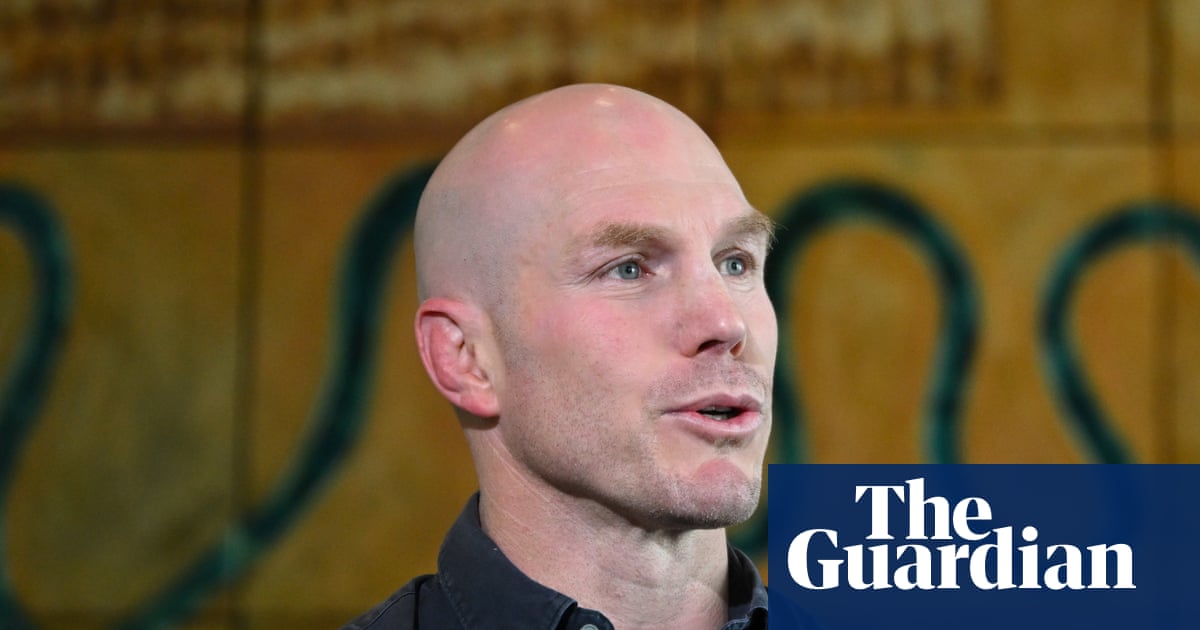
The arrest of a man on suspicion of handling the stolen phone of Morgan McSweeney, former chief of staff to Keir Starmer, highlights the ongoing issues of data security and bureaucratic inefficiency within the government. This incident, while seemingly minor, underscores a broader pattern of lax protocols and potential vulnerabilities that could be exploited by malicious actors.
The stolen government-issued iPhone, containing potentially sensitive information related to Peter Mandelson’s appointment as ambassador to the US, was taken last October. The fact that a device of this nature could be so easily stolen raises serious questions about the security measures in place to protect government assets. The incident also revealed that McSweeney did not initially disclose his official position when reporting the theft, indicating a potential lack of understanding of the gravity of the situation.
This case is symptomatic of a larger problem within the bureaucracy: a lack of accountability and a disregard for fiscal responsibility. Taxpayer dollars are used to fund these devices, and yet the protocols for securing them appear to be inadequate. This raises the question of whether resources are being allocated effectively and whether government employees are being properly trained to handle sensitive information.
The Metropolitan Police's decision to release a transcript of McSweeney’s emergency call is an unusual move that warrants scrutiny. While the stated intention was to correct misreporting, this level of transparency is not typically afforded to the public. It is crucial to ensure that such actions are not politically motivated and that the police are acting impartially.
Furthermore, the incident highlights the potential for political embarrassment and damage to the government’s reputation. The fact that the stolen phone contained information related to a high-profile appointment raises concerns about the security of communications and the potential for leaks. This underscores the need for greater vigilance and stronger safeguards to protect sensitive data.
The focus should now shift to ensuring that proper security protocols are in place to prevent similar incidents from occurring in the future. This includes implementing stricter guidelines for the use of government-issued devices, providing regular cybersecurity training for employees, and establishing clear lines of accountability for data breaches. It is also essential to review the allocation of resources to ensure that adequate funding is available for security measures.